In the first part of this blog series we reviewed how unrelenting data growth, the increasing value of data and the transformation of application services are introducing increased complexity and risk into the data protection process.
In part two, we will examine how the increased distribution of data along with the maturation of artificial intelligence and machine learning technologies is adding further complexity to how critical data should be protected across Edge, Core and Multi-Cloud environments.
Trend 3: Distributed Data
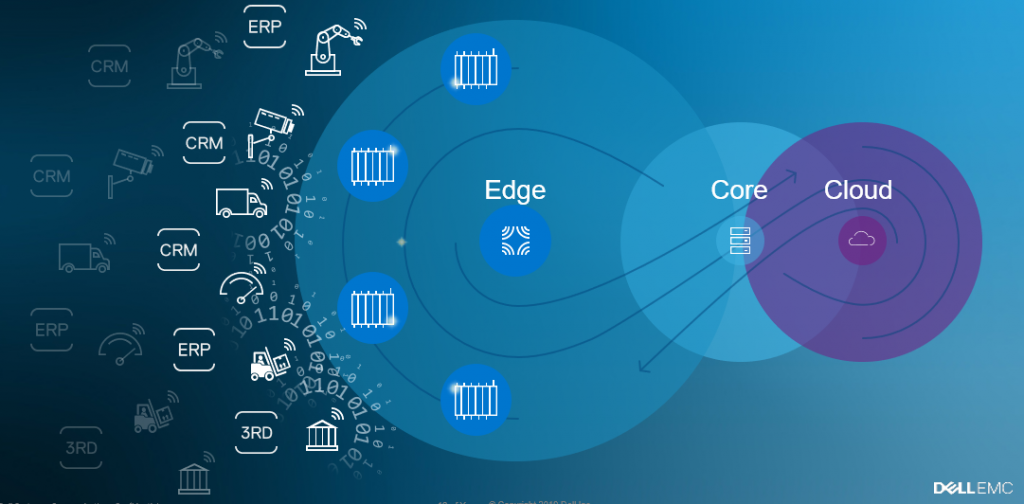
As the Internet of Things (IoT) drives intelligence deeper into the edge of the network, growth in data and the IT infrastructure itself will not be confined to just the four walls of the data center and the public Cloud. From autonomous vehicles and smart cities to automation on factory floors, data is being created at every conceivable corner around the globe. This data is stored and analyzed locally without being uploaded to a central data center or to the Cloud.
This distribution of compute, storage and code changes the game not only for the applications but also for data protection systems that can no longer rely on a centralized control server to manage protection for all the entities that make up an application service. If data is captured and analyzed at the edge, its importance is being determined there and therefore the level of protection required for it also needs to be applied there. Moreover, data is becoming ephemeral and predefined data protection policies may not apply anymore.
One example of this would be the video feed from a connected car. Typically, this data is deleted after a short period of time, however, if there is an accident or the car is stolen, the value of the video dramatically increases. In this instance, the video should be immediately protected and replicated to the core data center. A traditional, centralized data protection control plane cannot manage this type of a distributed environment that could potentially constitute many thousands of individual endpoints. Consequently, data protection implementation methods need to change.
Trend 4: Artificial Intelligence and Machine Learning
The fourth trend is the growth in artificial intelligence and machine learning (AI/ML) technologies. For centuries machines worked for humans, but now we have entered an era where intelligent machines work alongside humans.
Humans, in many cases, are guided by machines and interact with them similarly to how they engage with other humans. Digital assistants, navigation systems, auto-pilots and autonomous cars are just a few examples[1]. Such new models of interaction between humans and machines will become the norm not only in our daily life but also in how we operate IT systems. Users who grew up talking to Siri or Alexa will be the next generation of application developers and IT system administrators. The solutions deployed in the Cloud, data centers or Edge will need to evolve to enable user interaction using natural language and to automate most of the mundane work, leaving the users/administrators to perform high-level guidance and exception handling.
So how will these four mega-trends impact and change the data protection solutions of the future? In Part 3, we will discuss the four pillars of future data protection management.